Elevate your digital security with our advanced cybersecurity platform, offering robust protection against the dynamic threats of cyberspace. We specialize in comprehensive penetration testing for Web Applications, APIs, Mobile Apps and Networks, our state-of-the-art solution and experienced team work together to fortify your defenses, ensuring the utmost security for your digital assets and networks.
I'M INTERESTED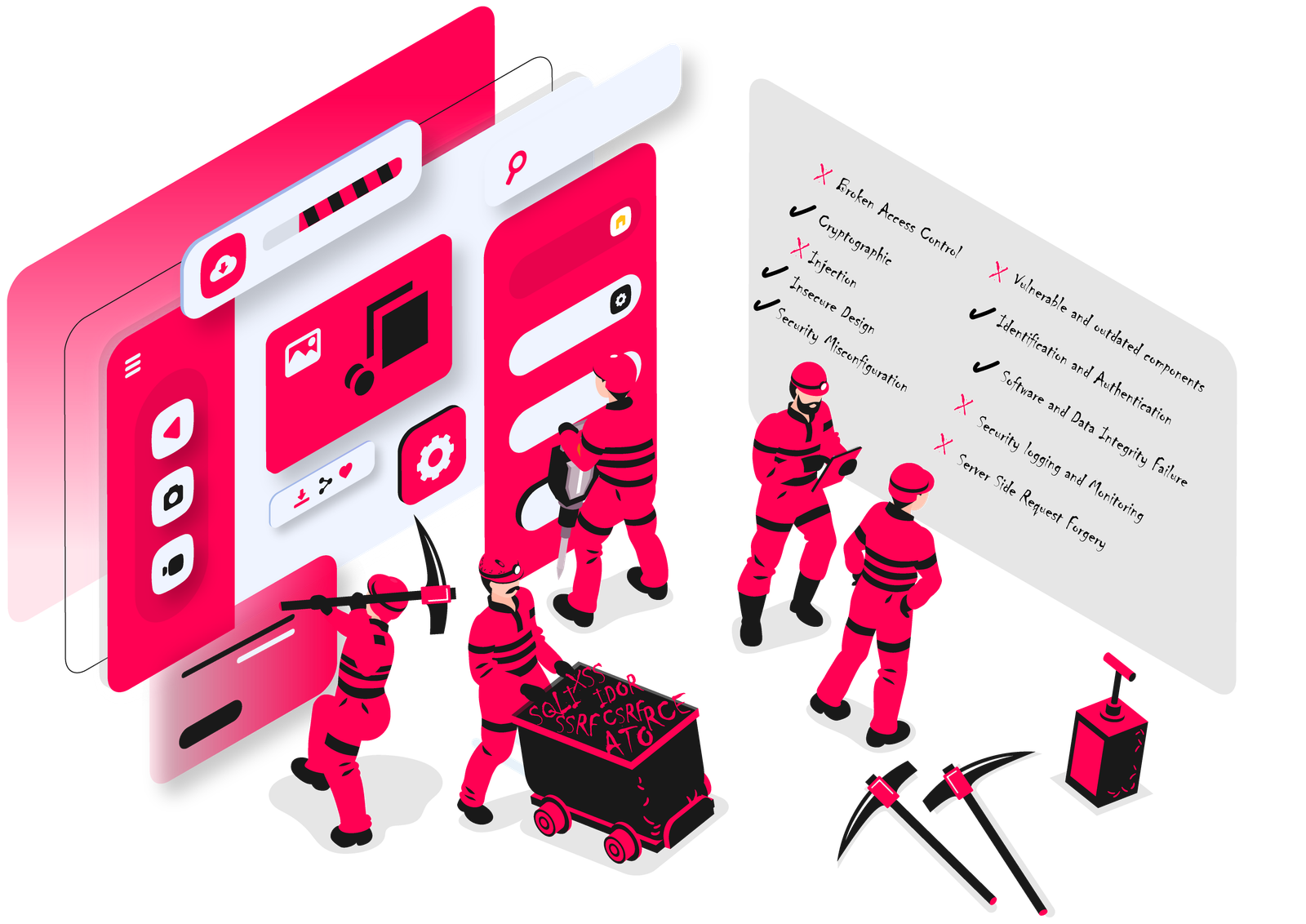
We Strengthening Businesses Against Threats by Unmasking Real-World Vulnerabilities
The following highlights the most prevalent enterprise motivations for vulnerability assessments:
Unveil flaws, and discover previously unknown vulnerabilities — exploring how they may be exploited.
Safeguard the organization and its clients by identifying and mitigating potential vulnerabilities that could lead to security breaches.
Validate and ensure the effectiveness of existing security controls in place to protect sensitive information.
Ensure the overall safety and integrity of systems by identifying and addressing vulnerabilities that could compromise their functionality.
Conduct assessments to test and strengthen the security of systems, ensuring the ongoing safety and resilience of the organization.
Improve confidence in cybersecurity by confirming that the design and architecture of systems meet high-security standards.
Our expert team follows the latest industry standards, including the OWASP Top 10 2023, ensuring rigorous testing to identify and mitigate security risks. Partner with us for comprehensive assessments, actionable insights, and robust protection for your web applications. Our testers conduct a meticulous analysis of the application, emphasizing critical aspects such as:
• Authentication and Authorization
• Input Validation
• Session Management
• Error Handling
• Cryptography
• Business Logic Testing
• Output Encoding
• Client-Side Testing
We recognize the vital role APIs play in your digital ecosystem. Our certified security professionals specialize in API penetration testing, meticulously assessing the resilience of your APIs. Trust us to ensure your APIs are robust, reliable, and fortified against potential threats, securing your digital assets with precision and expertise. Our API penetration testing covers key security areas aligned with OWASP API standards, including but not limited:
• Encryption
• Authentication and Authorization
• Input validation
• Session management
• Rate limiting
• Mass assignment
• Security headers
• Logging & Monitoring
• API versioning
• Dependency analysis & Documentation
Elevate your mobile app security with FlawMiners. Our assessment covers client and server sides, aligning with the OWASP mobile assessment framework.
For API assessment, we conduct a web app penetration test following OWASP standards. We analyze network
protocols for data security, identify service endpoints, and assess for threats like privilege escalation and
injection flaws. Our testing includes but not limited:
• Static Analysis
• Reverse Engineering
• Network traffic analysis
• Authentication review
• Tampering/reverse engineering
• Storage mechanism
• Web service/API analysis
Our Network PenTesting integrates industry best practices for effective risk reduction and compliance. Through four key phases—Reconnaissance, Enumeration, Documentation, and Exploitation—executed cyclically, we build on findings and uncover potential risks. This streamlined approach ensures comprehensive coverage and delivers meaningful results, Our testing includes but not limited :
• Discover assets
• Identify leaks
• Investigate breaches
• Enumerate assets
• Explore acquisitions & scan targets
• Document services & review exposure
• Check config. & analyze errors
• Conduct automated
• Test bypasses
• Check misconfiguration
• Check credentials
• Check cross-reference versions
• Find sensitive
• Conduct brute-force
With great pride, we showcase our achievements in the realm of cybersecurity, where we've successfully identified and addressed critical vulnerabilities within industry giants such as Google, Meta, Microsoft, Adobe, Firefox, Amazon, Apple, ebay, avast and many others.
Let's answer some questions about us!
Don’t hesitate to reach out if you have any questions
With over 8 years of invaluable experience, FlawMiners has solidified its position as a trusted authority in cybersecurity. Our journey commenced in the realm of bug bounty programs, where we fostered collaborative partnerships by uncovering critical vulnerabilities with industry giants such as Google, X (Twitter), Apple, Meta (Facebook), Microsoft, Adobe, Mozilla, eBay, and more than 50 other companies. Building on this extensive background, our expertise in cybersecurity is deeply rooted in practical knowledge gained over the years.
Our journey began in the world of bug bounty programs, where we collaborated by discovering critical vulnerabilities with industry giants such as Google, X (Twitter), Apple, Meta (Facebook), Microsoft, Adobe, Mozilla, eBay and more than 50 other companies. Our expertise in cybersecurity is grounded in this extensive experience. What sets us apart in penetration testing is our focus on uncovering real-time security vulnerabilities actively exploited by malicious actors.
Strengthening Businesses Against Threats by Unmasking Real-World Vulnerabilities.
Exercising precision in testing, unwavering integrity in decision-making, and ensuring absolute confidentiality in handling sensitive data.
With over 8 years of cybersecurity prowess and a foundation in bug bounty programs, we stand out as your trusted penetration testing partner. Our track record includes submitting hundreds of critical vulnerabilities to industry giants, showcasing our expertise in unmasking threats. When you choose us, you opt for a seasoned team dedicated to fortifying your cybersecurity defenses with unparalleled experience and insights.
Let us know if you want to talk about one of our services
Feel free to reach out and connect with us. We're here to answer any questions you may have. Whether you're seeking information, have inquiries about our services, or just want to say hello, we'd love to hear from you.
services@flawminers.com